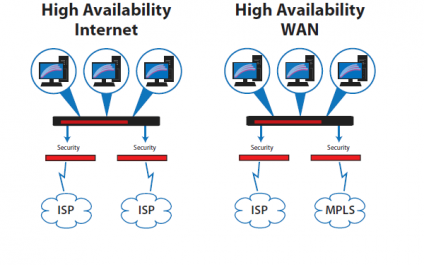
An application of software-defined networking (SDN) that is applied to WAN connections and used to connect enterprise locations across vast geographic distances. It connects branch offices, data centers, and other business sites to a central corporate network, using a software approach.
Blogs
New developments, innovations, and reporting from around the IT sector
How To Improve Cybersecurity In Your Business
SD WAN
Organizations have become so dependent on technology that when applications become unavailable, we often see employees pack it in and go home for the day.
Most all organizations have become extremely technology centric relying on the availability of business critical cloud/SaaS applications, email, voice/video collaboration, web access and more.
VPNFilter Malware Threat Continues To Grow

VPNFilter malware wreaks havoc on routers, check if you're affected
VPNFilter, a recently discovered malware that attacks routers and switches, is far more dangerous than originally thought.
Cisco Talos, which first posted information about VPNFilter in May, has now updated its blog with new findings about this threat, and the results are not good.
Equifax Breach Caused By Failure to a Patch Server?

Are you kidding me?
Not that surprising actually. The vast majority of cyber security breaches are due to unpatched servers.
How can you be certain that your servers and applications are up to date and secure?
NetWatchman Server Care ensures that all of your systems will be fully patched and updated with the latest stable code available.
Elements of a Strong Information Security Program
Now more than ever, businesses are facing attacks on the digital front that threaten to steal their data and leak confidential information. Organizations today are coming to the frightening realization that they need to either invest in a proper security program or wait until the inevitable hack that puts them out of business.
An Overview Of Penetration Testing

Penetration Testing is a Critical Part of Any Cyber Security Program
An Overview Of Penetration Testing
Penetration testing provides an accurate evaluation of your organization’s risk for data breach.
Penetration Testing means a test methodology in which assessors attempt to circumvent or defeat the security controls of an organization’s IT systems and networks.
3-2-1: Easy Steps to Back Up Your Data

Files on a computer can represent anything from years of work to irreplaceable mementos of times past, all of which can vanish without a trace if the worst happens and your equipment fails. The result of losing that data can range from a tragedy to a significant financial loss, and in a world where any number of unforeseen problems can destroy hard drives and other equipment without a moment's notice, it pays to be prepared for catastrophe with data backups.
What Is the Difference Between a Differential and an Incremental Backup?
Your Company’s Hidden Computer Security Weaknesses

As much as information technology (IT) has improved commerce and the business world, it also creates the potential for malicious damage. While computer networks enhance communication and data sharing and make business more productive, they also present an opportunity to access corporate information.



